When adding high availability to a Lync Server Edge
Server deployment, an organization must make a decision about how it
will provide load-balancing features. The only options available for
load-balancing Edge Servers are to use DNS-based load-balancing or to
leverage a hardware load-balancing solution.
Note
Windows Network Load Balancing (NLB) is not supported
for load balancing any of the Lync Server roles, including Edge Server
features.
DNS load balancing seems like an attractive feature
at first, but does have some limitations. Organizations should review
these limitations and then make a decision about whether a hardware load
balancer is required. The main limitation of DNS load balancing is that
it does not work with some features or legacy endpoints, including
Endpoints running previous versions of the Communicator client
Federated organizations running previous versions of Communications Server
Not all organizations are affected by these
limitations and might still be able to deploy DNS load balancing for
their Lync Server infrastructure.
Hardware Load Balancer
Using a hardware load balancer comes at a greater
cost than DNS load balancing, but adds some flexibility and backward
compatibility that an organization might require. Configuring the
hardware load balancer is typically the most difficult part of an Edge
Server deployment simply because of how flexible the load-balancing
software generally is.
Some basic guidelines must be followed when using a hardware load balancer for Edge services:
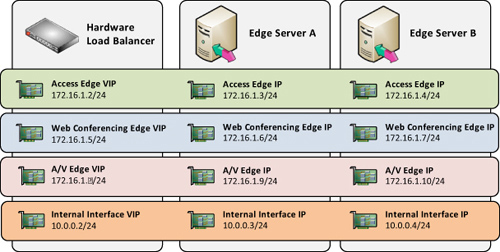
To summarize the requirements, if an organization
deploys two Edge Servers with a hardware load balancer, it needs nine
publicly routable IP addresses: three for the virtual IP addresses and
three for each Edge Server. That logical configuration is depicted in Figure 1.
In
addition to the public IP addressing requirements, there are some
stipulations about what type of Network Address Translation (NAT) must
be configured on the load balancer. For traffic from the Internet to the
server, the hardware load balancer must use Destination Network Address
Translation (DNAT).
This means that as a packet is received from the
Internet to the virtual IP address, the hardware load balancer rewrites
the packet to change the destination IP address to one of the IP
addresses actually assigned to an Edge Server network adapter.
Note
The fact that the term NAT
is used here does not imply that the Edge Server uses private IP
addresses. Even though the Edge Server has a public IP address, the load
balancer must still translate requests to the virtual IP address to an
IP address actually assigned to an Edge Server.
For traffic from the server to the Internet, the load
balancer must be configured for Source Network Address Translation
(SNAT). This means that packets sent outbound from the Edge Servers are
translated by the load balancer back to the virtual IP address that the
external Internet clients expect to communicate with.
Hardware Load Balancer Configuration
This section discusses the hardware load balancer
configuration for an Edge Server. There are two perspectives to look at
for load balancing Edge Servers because the external-facing adapter and
internal-facing adapter have their own requirements. An Edge Server must
be load balanced on both sides to function properly, but each side has
slightly different requirements.
Warning
Many load balancers have the option to balance “All
Ports” for a given pool. Avoid this configuration, no matter how
tempting and easy it seems. Instead, load balance only the ports found
in the tables that follow.
Starting with the external interfaces, the load
balancer should have three publicly routable virtual IP (VIP) addresses:
one for the Access Edge, one for the Web Conferencing Edge, and one for
the A/V Edge. These three virtual IP addresses map to the three public
IP addresses configured on each Edge Server. So, the VIP used for Access
Edge maps to the real IP addresses for each Edge Server’s Access Edge
service, and the same goes for the Web Conferencing Edge and A/V Edge
services. Depending on the load balancer configuration, this usually
requires three separate pool objects, as depicted in Figure 2.
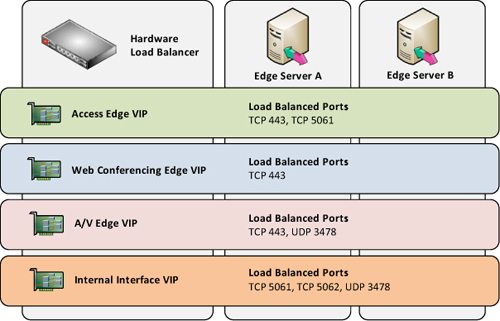
Table 1 outlines what ports must be load balanced to each virtual IP address.
Table 1. External Edge Interface Load Balancing
| Virtual IP Address | Port | Function |
|---|
| Access Edge | TCP 443 | Remote access |
| Access Edge | TCP 5061 | Federation and Public IM |
| Web Conferencing Edge | TCP 443 | Remote web conferencing |
| A/V Edge | TCP 443 | STUN |
| A/V Edge | UDP 3478 | STUN |
After
configuring the external interface load balancing, the internal adapter
configuration must be completed. Unlike the external adapter that uses
three virtual IP addresses, only a single virtual IP address is required
for the internal adapter because each Edge Server has only a single IP
address for its internal adapter.
Table 2 outlines what ports must be load balanced to each virtual IP address.
Table 2. Internal Edge Interface Load Balancing
| Virtual IP Address | Port | Function |
|---|
| Edge Internal Interface | TCP 5061 | Signaling |
| Edge Internal Interface | TCP 5062 | A/V Authentication |
| Edge Internal Interface | TCP 443 | STUN |
| Edge Internal Interface | UDP 3478 | STUN |
Note
There is no entry here for load balancing the
internal Web Conferencing Edge interface. That is not an omission or
error; port 8057 on the internal interface should not
be load balanced by the hardware load balancer. The Front-End pools
automatically distribute requests to multiple Web Conferencing Edge
Servers if configured. Don’t forget to include TCP 8057 in the firewall
rules, though, because even though it’s not load balanced, the Front-End
servers need to be able to reach that port on Edge Servers.
DNS Load Balancing
If the limitations of DNS load balancing described
earlier don’t pose any issues to an organization’s Lync Server
deployment, the organization can proceed with that method instead of
purchasing a hardware load balancer. There are actually some advantages
to using DNS load balancing, mainly the simplicity involved in
configuring the load balancing that just involves using multiple A
records for the same name in public DNS. Table 3 shows the DNS records required to achieve DNS load balancing.
When using DNS load balancing, the Edge Server can
use private IP addresses that are translated by NAT for all three roles
including A/V Edge. This is a big advantage for organizations that might
not have many public IP addresses available because when using DNS load
balancing, there is no virtual IP address requirement.
In other words, DNS-based load balancing requires
three fewer IP addresses than a hardware load-balancing solution. Each
Edge Server IP still needs to be mapped to a unique public IP address if
it is being translated by NAT, but there is no idea of a virtual IP
address in this type of solution. In fact, when using DNS load
balancing, Microsoft recommends using NAT for the IP addresses bound to
the Edge Server network adapters.
Another advantage of DNS load balancing is that the
native server-draining feature in Lync Server is available. This enables
administrators to prepare a server by maintenance through the Lync
Server Control Panel the same way as the other roles.
In some organizations, the team responsible for Lync
Server might not be the same team that manages the network and hardware
load balancers, which can make it difficult to coordinate preparing a
server for maintenance. Instead of the Lync Server administrators
quickly draining a server’s connections, they might need to submit a
request to have the network team drain the load balancer connections for
a particular node and then check back later to determine whether the
connections have cleared.
Sometimes this separation of teams can be just as
efficient as one person having complete control, but often times it
slows down the maintenance process.
Note
Although DNS load balancing is available for Edge
Servers, keep in mind that the reverse proxy for web component services
is a critical piece of remote access. Load balancing for a reverse proxy
must be addressed separately and can either be done with a hardware
load balancer or possibly through Windows Network Load Balancing (NLB)
for Microsoft Forefront Threat Management Gateway or Unified Access
Gateway.